It's a testament to IT teams across corporate Australia, just how smoothly an entire nation of office workers has made the monumental shift to remote working. But now the workforce is successfully connected, what should IT teams be focused on next?
The first priority was connectivity
It was no easy feat, and yet literally within the space of 10 days, millions of Australians made the move from the office to remote working. Take a bow, IT teams right across corporate Australia.
Most companies had the underlying infrastructure to make work from home a possibility. The speed at which this has been deployed highlights how ready IT teams were for this change and how successful IT teams have been in managing the shift.
What comes next ?
So, the first priority for organisations has, in the main, been achieved. People have connectivity - to each other, to customers, and to the office network for critical files and collaboration.
Now the most critical gap has been plugged, what are the next priorities ? Here's our top six.
Priority 1. Visibility
Visibility comes first because it is key to mitigating risk and to implementing all other priority tasks.
Visibility of the network, visibility of mobile devices, visibility of end user behaviour, visibility of costs being incurred. All of these are critical to ensuring a secure, stable, fit for purpose, and cost effective ongoing working from home operation.
Visibility of the network includes knowing who is accessing, by what device, for what purpose; and ensuring that the network has the accessibility and bandwidth to cope.
Visibility of mobile devices is an essential component of network security, and cost control. The mobile threat landscape is a significant risk with the mass move to WFH. Visibility of mobile devices will detect threats such as malware, and security lapses such as non-compliant devices. It will inform understanding of how employees are using the device, allowing data consumption to be monitored, and costs to be monitored.
Visibility of end user behaviour is useful for identifying human threats to the network, for understanding the individual costs incurred, and for supporting end user productivity. Employees are a company’s greatest asset and biggest threat. Devices are more than extensions of the computing infrastructure, they are extensions of the end user. Ultimately it is the end user who delivers both productivity and threats to the network, not the device.
Visibility of costs for many IT teams comes well down their list of priorities, but that approach can be short-sighted. IT business leaders understand the importance of protecting the bottom line and ensuring a responsible approach to cost control. The new WFH scenario has significant potential for cost blow-outs due, in the main, to increased data consumption, and data storage. This cost can be both financial and reputational.

Priority 2. Security
The threats to the network infrastructure and to corporate data are greatly magnified by the sudden WFH scenario.
The need for reliable connectivity was obvious – but the need for enhanced cybersecurity and data protection systems is now the most pressing concern.
Microsoft has reported that every country in the world has seen at least one COVID-19 themed attack (see map below). The tech giant said the "volume of successful attacks in outbreak-hit countries is increasing, as fear and the desire for information grows."
The sudden and exponential increase in remote working has created a unique new set of mobile, network and data protection challenges.
The mobile threat landscape has expanded. Remote workers create infinite new access points for hackers to exploit. Employees entering their email systems from remote locations also increase the possibility of clicking on sinister links, compromising existing cybersecurity systems.
Prior to the pandemic, many enterprises had strict rules prohibiting employees from connecting to corporate networks from home. In most cases those have been hastily set aside. Many organisations have no choice but to allow employees to connect to centralised corporate networking through home devices on home networks. This directly correlates to increased risk in managing the growth in physical, logical connections to the organisation's operating environment.
Aside from the network itself, the biggest threat is to data security. Accessing data, sharing data and storing data from remote locations are all threat vectors. Data leakage - unintentional more than malicious - can easily occur through use of remote printer-sharing, remote desktop file-sharing, and remote USB connections. The use of personal devices equals a real chance of delivering ransomware into the office network and allowing company data to leak out.
Priority 3. Network Stability
Network stability is closely aligned with the ability to scale bandwidth to accommodate fluctuating demand. With empty offices, the numbers accessing the corporate network through a business VPN is greater than it has ever been and some VPNs have been overwhelmed.
High-capacity VPNs are essential for companies seeking to continue their work, and organisations that are less well equipped will eventually succumb to the increased load. Adapting a highly developed network infrastructure, that will handle the escalating and fluctuating use will enable operational stability.
Priority 4. Support
Support - both providing it to remote employees and supporting internal IT teams so that they can focus on delivering critical services - is a priority.
Employees who don't usually work from home, or who are performing roles that are new to them, can quickly become unproductive and frustrated if unable to access support when their devices are not working as they did in the office. They may also need support in troubleshooting connectivity issues, or if they fall victim to malware or a phishing scam.
How is IT going to provide swift resolution for end users if they have their hands full holding the whole house together? It should never be a choice between delivering support to end users and focusing on strategic operational tasks.
Priority 5. Productivity
Everyone's at home and connected to the network. Tick. Everyone can access vital files and critical applications. Tick. But now the basics are in place, productivity will demand a shift to the next level. Collaboration as if we were all still in the same room is the goal.
Some organisations can skip this priority. Enterprises with a global or national presence, or who already had a remote workforce, are likely to have effective collaboration tools in place. The rest of us have Zoom!
Which is a case in point. Zoom users surged by millions as it was downloaded by every man and his dog in the early days of social distancing. Now just a couple of weeks later we are seeing corporates shifting away from Zoom, warning or even banning employees from using the platform altogether due to security concerns.
Finding a collaboration tool or suite of tools may not be high on the list of the IT team, but it will be high on the list for employees, which makes it a priority for business operations.
Priority 6. Cost Control
Organisations have been impacted by this pandemic is varying ways dependent on the industry vertical they occupy. Cost control may be less or more important in the short term, according to individual circumstances.
Industries experiencing a massive slowdown or shut down of services will be looking to minimise all costs. Industries that have ramped up to meet increased demand are more likely to prioritise operations over cost.
Short term it may be a case of the 'Nike Principle' - just do it! Get the systems up and running that allow the organisation to operate at whatever level is required. But, in the longer term, cost control will inevitably be important to all organisations.The potential for significant cost blow-outs is real. In the short term the threat is seen most obviously in the form of increased data consumption.
And now some answers...
There may not be one solution which plugs all the gaps for an organisation, but there may be one or two tools that can go a fair way to covering off a number of concerns.
UEM
A Unified Endpoint Management platform could be a quick and inexpensive option to cover off endpoint visibility, security, remote support and cost control. UEM is an evolution of enterprise mobility management and in the past two years has evolved to incorporate all endpoints including laptops, desktops, gateway devices and edge devices.
There are a number of excellent UEM products available, and these can be tailored to suit organisations of various sizes. Some market leading vendors include VMWare AirWatch/Workspace One, SOTI and MobileIron. Microsoft Intune is the best choice for companies with Microsoft tools like O365. Some Telstra mobile plans come with UEM licences included. Read more
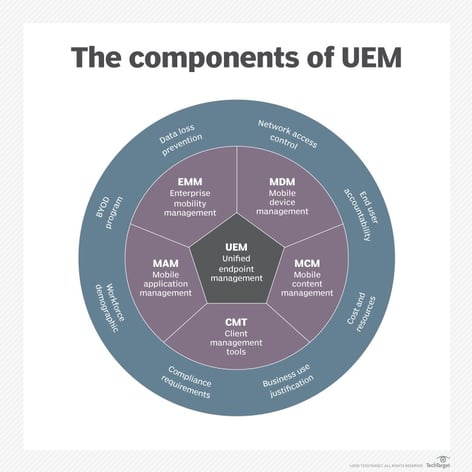
Digital Workspace
Digital Workspace and UEM as terms which are are often used interchangeably. VMWare has pushed the language of digital workspace by calling their SaaS product, Workspace ONE. A digital workspace is a term to describe the collapsing of mobile and Desktop OS management, application delivery, and access management into the one platform. It is perhaps broader than UEM, in that it also focuses on the delivery of unified communications tools. Microsoft Office365 delivers a digital workspace environment. Read more
Wandera data compliance and threat management
Wandera is a cloud-based data policy and compliance platform which assists in the management of mobile data consumption and optimisation through a number of features including data capping, content filtering and even tethering (mobile hotspot) management. MobileCorp is a Wandera partner. Read more
NextDay Connect
NextDay Connect is a solution originally developed in response to customer demand for reliable connectivity while waiting on nbnTM transition. However, it soon became apparent it was relevant to Covid-19 remote working connectivity. NextDay Connect was developed by MobileCorp in partnership with Telstra and Cradlepoint and utilises Cradlepoint 5G routers to deliver instant (next day) reliable mobile connectivity with dual SIM redundancy. In the United States Cradlepoint routers have been used to connect mobile Covid-19 testing centres. This solution would be suitable for a critical communications remote hub or VIP connectivity. It comes with zero-touch deployment and remote management. Read more
Telstra Programmable Network
TPN is Australia’s first 'Network as a Service' solution. It is a globally connected on-demand networking platform and an ideal solution for scalable remote workforces. Telstra Programmable Network is designed to deliver secure, flexible and on- demand connectivity to virtual network services with automatic provisioning in minutes. Read more
Telstra Connected Workplace
Telstra Connected Workplace is Telstra's solution to a geographically-diverse workforce. It was designed as an all-inclusive solution for multi-site businesses, providing network connectivity, data, and a unified communication suite of services. The pitch is to do away with the complexity of managing separate plans, providers, platforms, applications, and invoicing. Combine all requirements into one platform with a single bill. Read more

About MobileCorp
MobileCorp is an enterprise ICT solutions company with a mission to keep our customers connected and productive with innovative and reliable communications technology solutions. Read About Us or Contact Us to discuss your changing needs in this unexpected and challenging pandemic world.
Have time to up-skill your knowledge?
If you are in sheltering in place and have extra time available, you might like to invest in up-skilling your knowledge by reading our Guide to Five Emerging Technologies for Australian Business. This guide provides an Australian perspective and information relevant to our marketplace.
We think these five technologies are worthy of your time investment, because when this crisis has passed, the Recovery will offer a new appetite for digital transformation.
UEM Michelle Lewis 16 Apr 2020
Related Posts
Popular Tags
- Mobile Devices (78)
- Mobility (70)
- Telstra (61)
- MobileCorp Managed Services (52)
- 5G (50)
- Mobile Network (33)
- Apple (30)
- Cradlepoint (30)
- MobileCorp (30)
- iPhone (26)
- Remote Working (23)
- Networks (21)
- Network (17)
- Covid-19 (16)
- UEM (16)
- Mobile Security (15)
- Wireless WAN (13)
- Cyber Security (12)
- MDM (12)
- TEMs (9)
- Unified Comms (9)
- Cloud (8)
- Mobile Expense Management (8)
- Wandera (8)
- Mobile Device Lifecycle (7)
- Mobile Device Management (7)
- Android (6)
- Data Networks (6)
- Sustainability (6)
- Samsung (5)
- Digital Experience (4)
- IOT (4)
- Microsoft Intune (4)
- Network Security (4)
- Security (4)
- Unified Communications (4)
- Microsoft (3)
- Data (2)
- Government (2)
- Managed Desktops (2)
- Microsoft 365 & Teams (2)
- nbn (2)
- webinar (2)
- Blog (1)
- EMM (1)
- Emerging Technologies (1)
- IT Services (1)
- Retail (1)
- SD-WAN (1)
- Starlink (1)
- Telstra Services (1)
- video (1)